In the rapidly evolving landscape of artificial intelligence, mastering advanced prompting techniques for the latest large language models (LLMs) such as ChatGPT GPT-5.5 and Claude Mythos/3.5 is essential for practitioners aiming to unlock their full potential. This comprehensive handbook delves deep into sophisticated methods tailored for 2026’s cutting-edge AI models, focusing primarily on complex coding tasks, security analysis, and orchestrating multi-agent workflows. Whether you are a developer, security analyst, AI researcher, or prompt engineer, this guide offers an encyclopedic resource packed with dozens of prompt templates, detailed before-and-after examples, token optimization strategies, and robust prompt chaining methodologies.
As AI models grow more capable and intricate, traditional prompting approaches fall short in handling multi-layered tasks, nuanced reasoning, and multi-agent interactions. This article bridges that gap by providing practical, tested strategies to elevate your AI prompting mastery and achieve unprecedented levels of precision, creativity, and efficiency.
Understanding the Evolution of ChatGPT GPT-5.5 and Claude Mythos/3.5
The AI landscape in 2026 is dominated by the latest iterations of two flagship conversational models: OpenAI’s ChatGPT GPT-5.5 and Anthropic’s Claude Mythos/3.5. Both represent significant leaps in language understanding, reasoning capabilities, contextual memory, and API flexibility compared to their predecessors.
Key Architectural Enhancements
ChatGPT GPT-5.5 incorporates advanced transformer optimization, enabling longer context windows up to 64,000 tokens, refined memory retention through dynamic token-weighting schemes, and enhanced multimodal processing that integrates text with limited visual and tabular data inputs. These upgrades empower GPT-5.5 to handle extensive coding projects, multi-turn security audits, and detailed multi-agent orchestration with unprecedented fluency.
Claude Mythos/3.5 follows a complementary design philosophy emphasizing interpretability and safety, featuring an advanced constitutional AI framework. This model excels in complex ethical reasoning, vulnerability detection, and collaborative agent coordination. Mythos/3.5’s architecture supports adaptive prompt conditioning that modulates response style and depth based on task complexity.
Implications for Prompt Engineering
Due to these fundamental shifts, prompt engineers must transition from simplistic command-style prompts to layered, context-rich constructions. Effective prompting now requires intricate token management, strategic use of role-play and persona injection, and chaining of prompts that exploit both models’ strengths synergistically. This evolution also introduces new challenges such as balancing token budgets with output quality and orchestrating multi-agent workflows without response degradation.
For practitioners looking to harness these innovations in professional coding environments or security analysis domains, understanding the underlying model improvements is critical. This foundational knowledge informs the design of prompts that minimize hallucinations, reduce ambiguity, and optimize for real-world application constraints.
Advanced Prompting Strategies for Complex Coding Tasks
One of the most transformative applications of GPT-5.5 and Claude Mythos/3.5 is in advanced software development workflows. From generating entire code modules to debugging intricate algorithms, these models serve as powerful AI coding assistants. However, to fully leverage their capabilities, you must master advanced prompting techniques tailored for coding complexities.
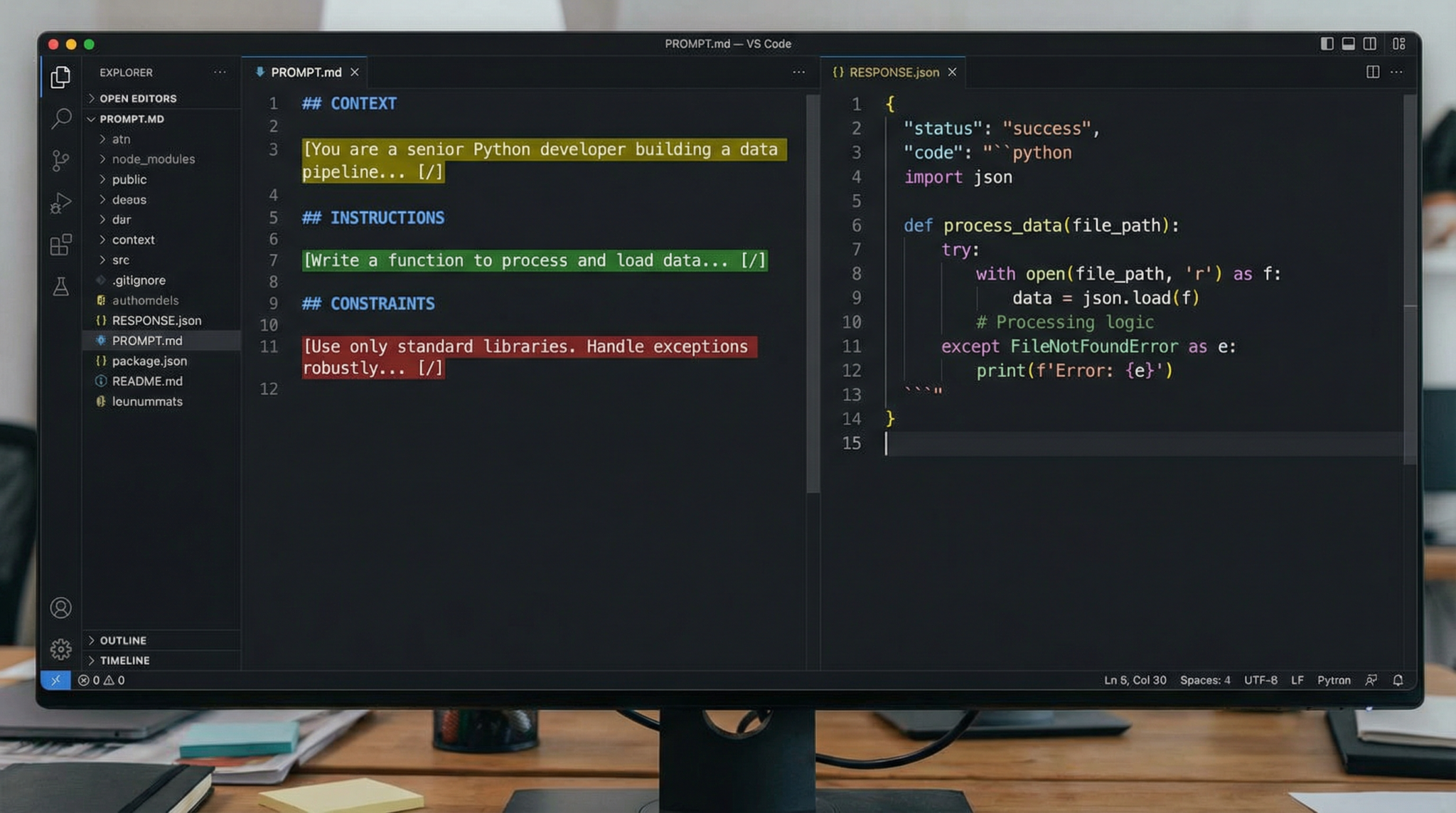
Prompt Structuring for Multi-Language and Multi-Framework Projects
Coding projects today often span multiple languages (e.g., Python, TypeScript, Rust) and frameworks (e.g., React, Django, TensorFlow). Effective prompts must explicitly specify the language, framework, coding style conventions, and expected output format. This reduces ambiguity and helps the model maintain consistency across diverse codebases.
- Example Template:
"Generate a modular Python 3.11 function using asyncio for concurrent HTTP requests. Adhere to PEP8 style guide, include type hints, and provide comprehensive docstrings."
This template ensures that the model understands the exact environment and stylistic constraints, resulting in more reliable, production-ready code.
Incorporating Code Comments and Documentation Dynamically
Prompting the model to generate detailed comments and documentation alongside code dramatically improves maintainability. Use role-injection techniques to “assign” the model a documentation specialist persona:
- Before: “Write a sorting function.”
- After: “As a senior software engineer, write a quicksort function in JavaScript with detailed inline comments explaining each step.”
Such persona-based prompting leverages Claude Mythos/3.5’s constitutional AI framework to produce clearer, more pedagogical explanations suitable for team collaboration or educational contexts.
Debugging and Code Review via Iterative Prompting
Advanced prompting includes iterative refinement cycles where the model reviews and improves existing code snippets. Using prompt chaining, you can feed the model code, receive suggestions, and then resubmit improved versions for further analysis.
- Prompt chaining example:
Step 1: "Review the following Python function for performance bottlenecks: [code snippet]" Step 2: "Apply your suggested optimizations and provide an improved version." Step 3: "Explain the changes you made and their impact on performance."
This multi-turn approach leverages GPT-5.5’s long context capability to maintain continuity and generate meaningful improvements.
Token Optimization Techniques in Coding Prompts
Given the high token consumption of code-heavy prompts, efficient token management is critical. Here are proven strategies:
- Use aliasing and abbreviations: Replace verbose descriptions with concise, standardized terminology.
- Leverage system prompt injection: Place global instructions in the system message to avoid repetition in user prompts.
- Employ selective context inclusion: Include only the minimal necessary code context rather than entire files to reduce token load.
- Split large tasks: Break complex coding problems into smaller sub-tasks handled sequentially by chained prompts.
These approaches allow you to maximize output quality while staying within the token budget, improving response speed and cost-efficiency.
Dozens of Coding Prompt Templates for GPT-5.5 and Claude Mythos
Below are selected prompt templates optimized for various coding scenarios:
- API Wrapper Generation: “Generate a TypeScript API wrapper for the OpenWeatherMap REST API with error handling and retries.”
- Unit Test Creation: “Write comprehensive Jest unit tests for the following React component: [component code].”
- Algorithm Explanation: “Explain the time complexity of the following merge sort implementation in detail.”
- Refactoring Legacy Code: “Refactor this legacy PHP code into modern Laravel 10 syntax with improved security and readability.”
- Multi-language Integration: “Generate Python and C++ interop code using Pybind11 to expose a C++ class to Python with detailed comments.”
To further enhance the reliability of your AI outputs and completely eliminate hallucinations, explore the comprehensive guide on Chain-of-Verification prompting, which offers detailed templates, examples, and practical applications for ChatGPT and Claude. This method is essential for practitioners aiming to elevate their prompt engineering, available through the Advanced AI Coding Prompt Templates.
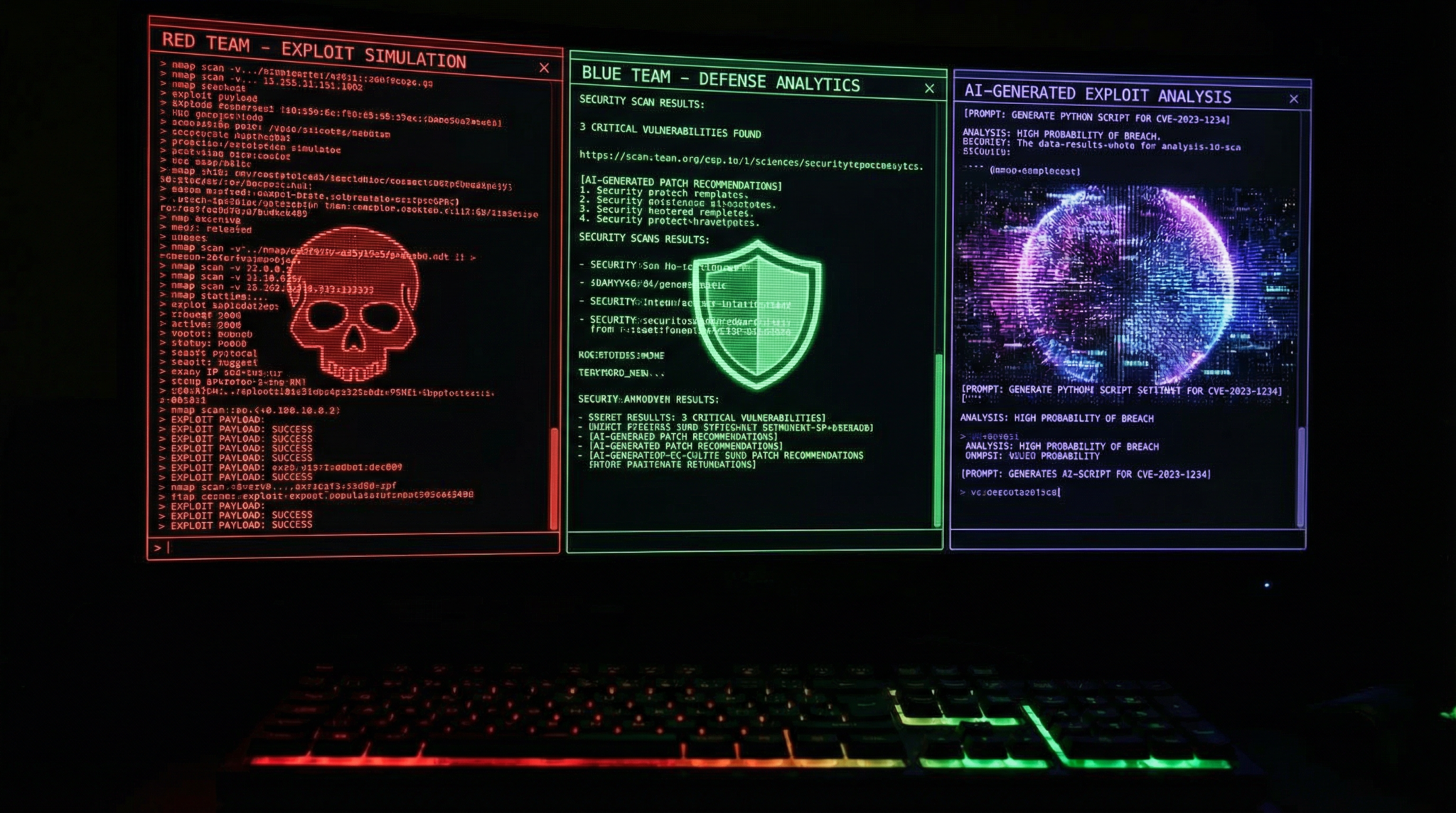
Security Analysis and Vulnerability Detection Prompting
Security remains a paramount concern in software development and IT operations. Leveraging GPT-5.5 and Claude Mythos/3.5 for security analysis requires nuanced prompting to ensure precise vulnerability identification, threat modeling, and remediation guidance.
Prompt Frameworks for Security Audits
Effective security prompting begins with defining the scope and type of analysis:
- Static code analysis: “Analyze the following code snippet for SQL injection, cross-site scripting (XSS), and buffer overflow vulnerabilities.”
- Threat modeling: “Identify potential threat vectors in this microservices architecture diagram described here: [architecture summary].”
- Security policy compliance: “Evaluate this IAM policy JSON for overly permissive roles and suggest least-privilege improvements.”
Claude Mythos/3.5’s safety-oriented design excels in these use cases by providing context-aware risk assessments and ethical considerations alongside technical findings.
Prompt Templates for Security Vulnerability Detection
Below are tested templates that produce actionable insights:
- “As a cybersecurity analyst, review this Node.js Express application code for OWASP Top 10 vulnerabilities and provide remediation steps.”
- “Perform a static analysis of this Solidity smart contract and highlight any potential reentrancy or integer overflow issues.”
- “Given this YAML Kubernetes deployment configuration, identify any misconfigurations that could lead to privilege escalation.”
Multi-Agent Security Workflow Orchestration
Modern security operations often require collaboration between multiple specialized AI agents to perform reconnaissance, exploit identification, and patch validation. Orchestrating these workflows through prompt chaining and role delegation maximizes efficiency and accuracy.
- Agent 1: “Perform passive reconnaissance on the target’s public IP range.”
- Agent 2: “Based on reconnaissance data, identify open ports and potential vulnerable services.”
- Agent 3: “Attempt to generate proof-of-concept exploits for identified vulnerabilities.”
- Agent 4: “Suggest patching strategies and validate their effectiveness.”
This multi-agent orchestration requires carefully crafted prompts that include explicit role definitions, data handoffs, and error handling instructions. To implement these concepts in practical coding environments, the Multi-Agent AI Security Workflows post offers a step-by-step tutorial on building custom OpenAI Codex plugins tailored for enterprise AI coding workflows, covering plugin architecture, security considerations, and deployment best practices.
Token Budget Management in Security Analysis Prompts
Security prompts can become token-heavy due to complex code snippets, detailed architecture descriptions, or multi-agent coordination. Some optimization tactics include:
- Summarizing code with syntactic abstraction to reduce token count while preserving semantic meaning.
- Using references to external documentation or prior prompt responses instead of repeating information.
- Segmenting analysis into discrete phases executed through prompt chaining rather than monolithic requests.
Balancing thoroughness with token economy ensures timely responses and cost-effective usage in real-world security environments.
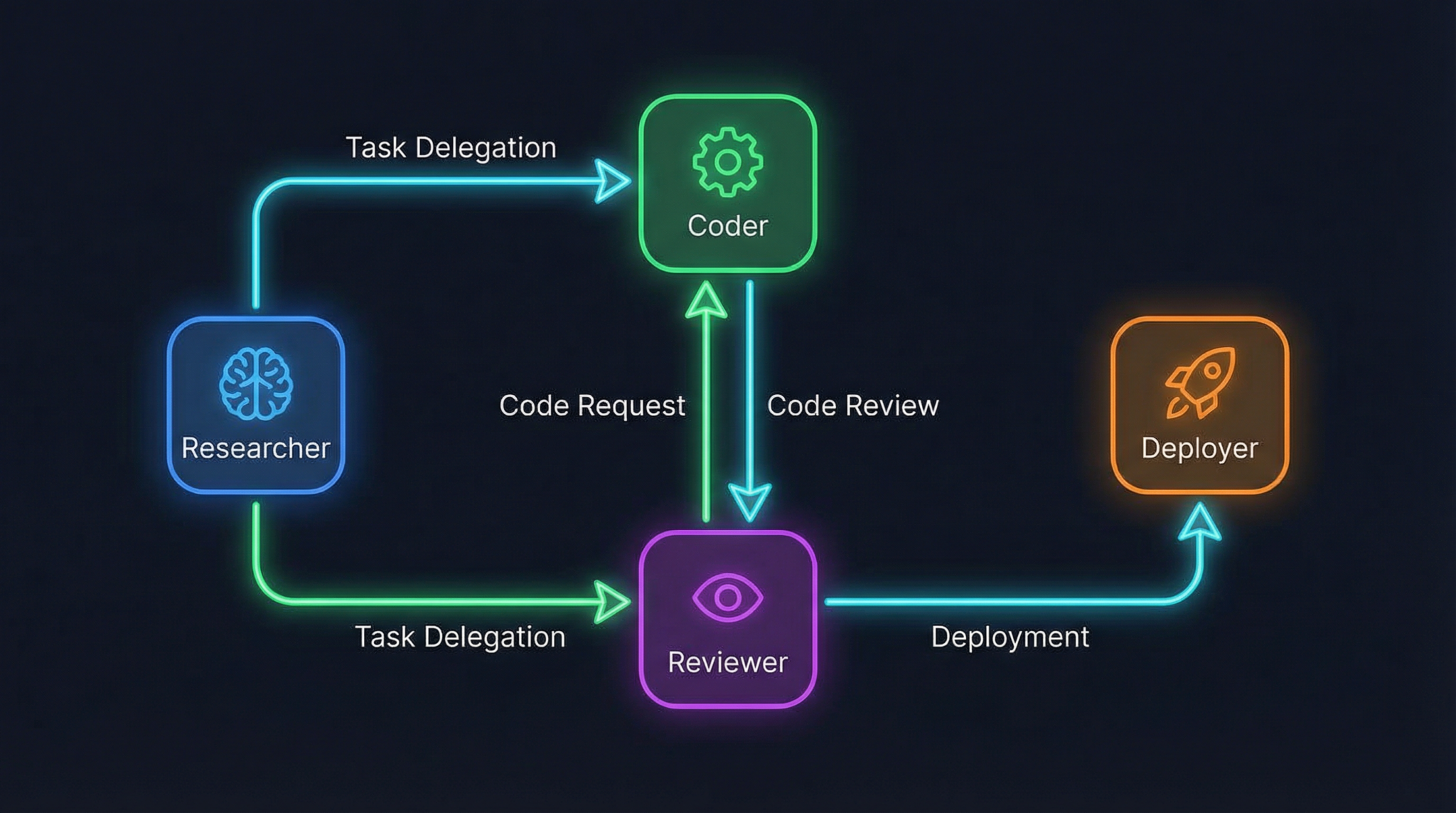
Orchestrating Multi-Agent Workflows with GPT-5.5 and Claude Mythos
Multi-agent AI workflows are revolutionizing complex task automation by enabling specialized agents to collaborate, each focusing on sub-tasks and passing refined outputs along a pipeline. Unlocking this capability requires advanced prompt engineering to define agent roles, communication protocols, and fail-safe mechanisms.
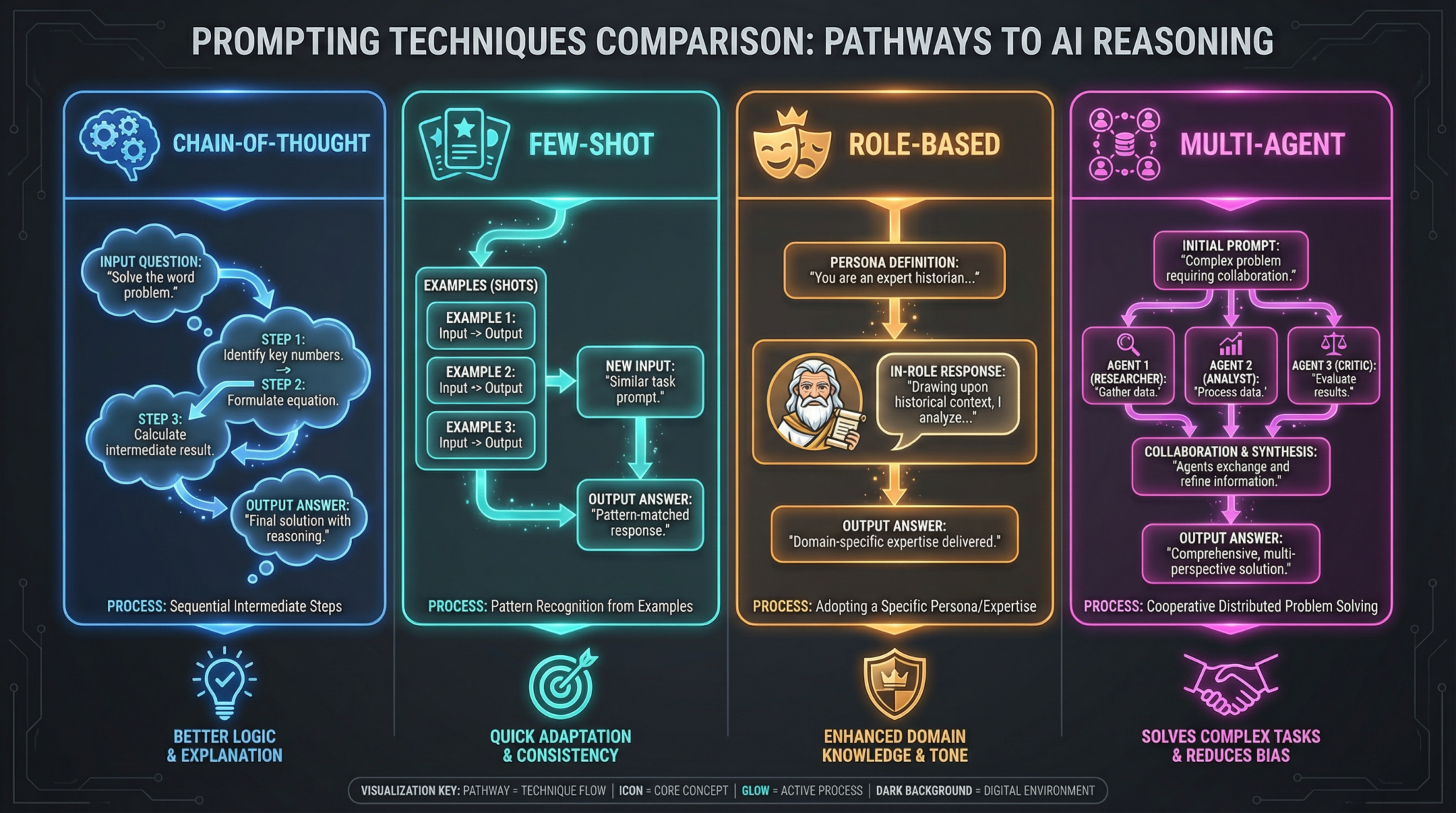
Foundations of Multi-Agent Prompting
Multi-agent workflows involve:
- Agent Role Definition: Clearly delineate the specific expertise and responsibilities of each agent within the workflow.
- Context Passing: Design prompts to pass relevant contextual data and outputs between agents to maintain coherence.
- Failure Handling: Embed fallback instructions and error detection to ensure robustness.
- Concurrency Control: Manage asynchronous or parallel agent operations to optimize throughput.
For example, a content creation pipeline could involve an agent for topic research, another for drafting, a third for editing, and a final agent for SEO optimization, each prompted with tailored instructions to perform their unique function.
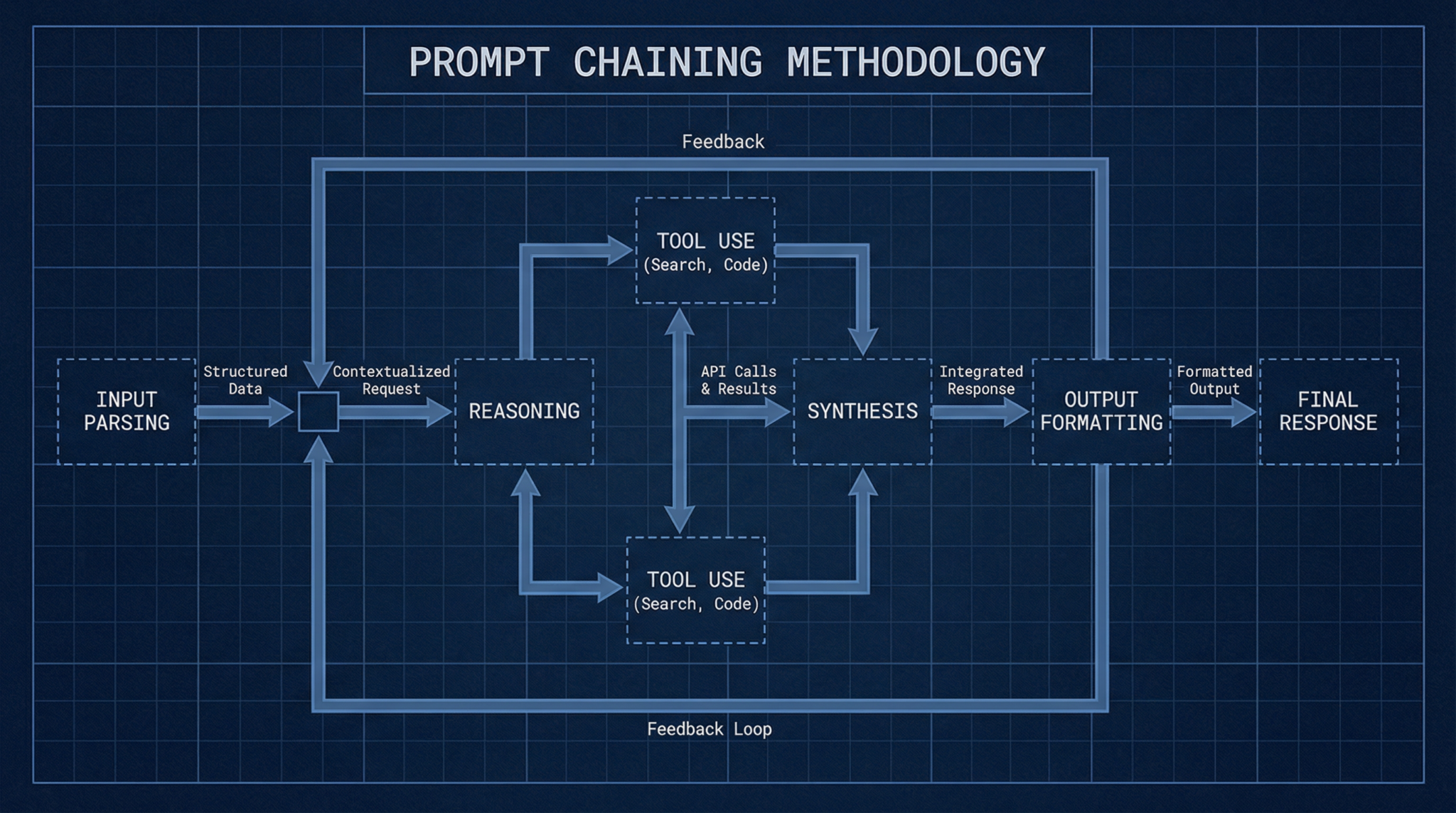
Prompt Chaining Methodologies
Prompt chaining is the sequential linking of prompts where each prompt builds on the output of the previous one. It is pivotal in multi-agent orchestration:
- Linear chaining: Each agent outputs data consumed by the next in a predefined order.
- Branching chains: Multiple agents work on parallel sub-tasks whose results converge downstream.
- Iterative loops: Agents revisit outputs for refinement until a quality threshold is met.
Implementing these chains requires careful prompt design to maintain context integrity and avoid token inflation. Leveraging GPT-5.5’s extended memory window is particularly advantageous for long chains.
Example Multi-Agent Workflow Template
Consider a software development lifecycle AI pipeline:
- Agent 1 (Requirements Analyst): “Extract and summarize key feature requirements from this product specification.”
- Agent 2 (Architect): “Design a modular system architecture based on requirements summary.”
- Agent 3 (Coder): “Generate initial code modules adhering to the architecture design.”
- Agent 4 (Tester): “Create test cases covering edge scenarios for generated modules.”
- Agent 5 (Security Auditor): “Perform vulnerability assessment on the codebase.”
Each agent receives the previous agent’s output as input, with prompts explicitly specifying the expected output format and style. This approach allows for scalable, distributed AI workflows capable of managing complex projects end-to-end.
While advanced prompting techniques enhance AI capabilities, generating effective inputs remains crucial for specific applications like naming businesses or domains. The article Multi-Agent AI Orchestration Best Practices presents a curated selection of ChatGPT prompts designed to help users craft compelling and creative business and domain names, demonstrating practical prompt engineering in action.
Dozens of Prompt Templates for Multi-Agent and Complex Task Handling
This section presents a curated selection of prompt templates engineered for multi-agent workflows and complex task orchestration, covering various domains such as coding, security, research synthesis, and content creation. Each template is annotated with usage notes and expected output structures.
Sample Multi-Agent Prompt Chain for Incident Response Automation
- Agent 1 (Alert Triage): “Analyze this security alert log and classify the incident severity with contextual justification.”
- Agent 2 (Investigation): “Based on the triage output, identify potential attack vectors and affected systems.”
- Agent 3 (Mitigation Planner): “Generate a prioritized mitigation plan with stepwise actions.”
- Agent 4 (Communication Lead): “Draft an incident report summarizing findings and recommended next steps for the security operations team.”
Prompt Templates for Token-Efficient Long-Form Document Generation
- “Generate a 3,000-word technical whitepaper outline on quantum computing advances, segmented into discrete sections with bullet points.”
- “Write the introduction section of the whitepaper with clear subheadings and references to recent research.”
- “Summarize the conclusion and future work sections emphasizing emerging challenges.”
Iterative Prompting Templates for Code Optimization
- “Analyze this C++ code snippet for memory leaks and suggest improvements.”
- “Rewrite the optimized code with detailed comments on the changes.”
- “Explain the trade-offs introduced by the optimizations.”
These templates serve as building blocks for more complex prompt chaining and multi-agent orchestration schemes. By tailoring them to your specific domain and use case, you can achieve scalable and maintainable AI-powered workflows.
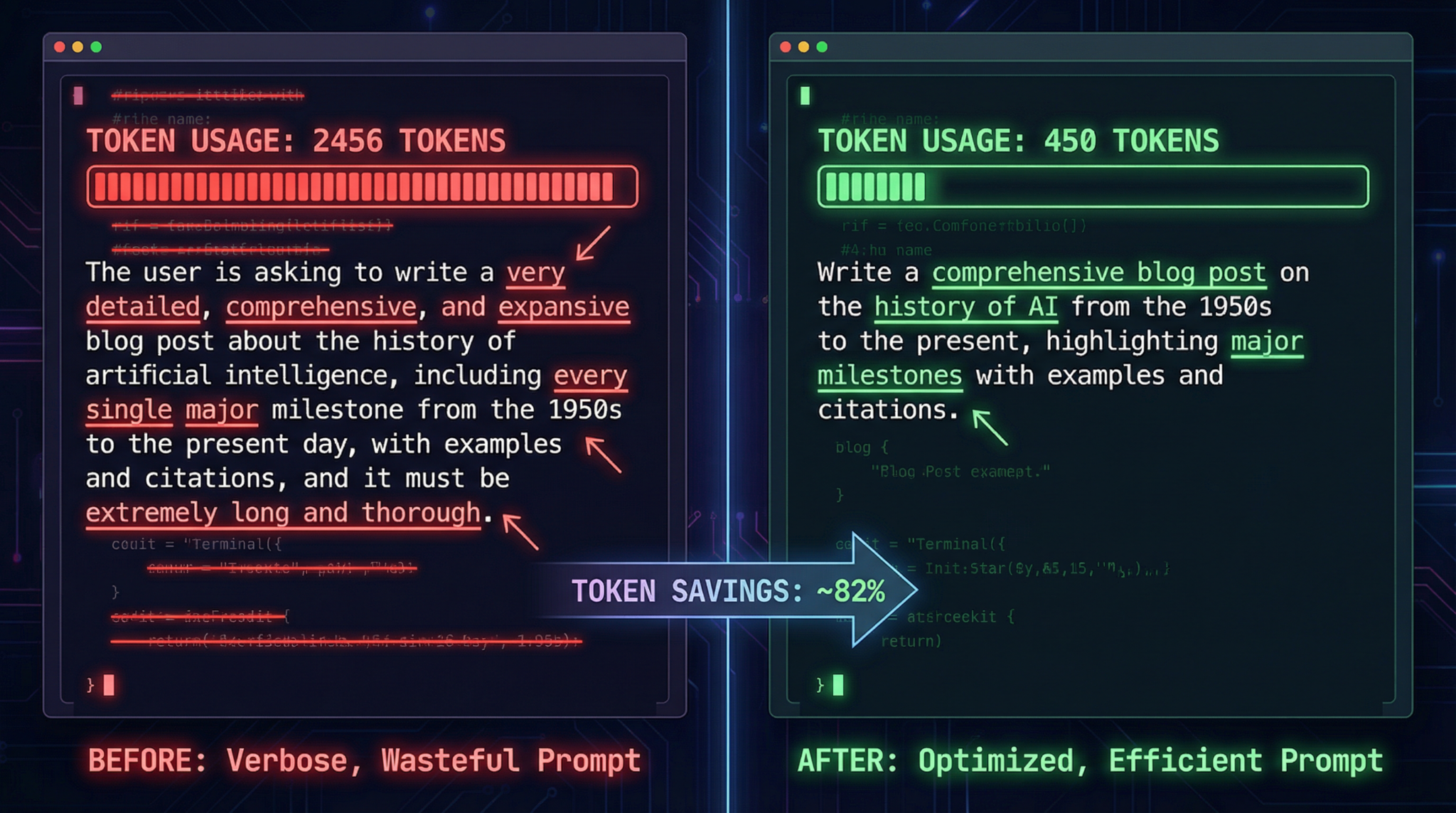
Token Optimization Strategies for Maximizing Model Efficiency
Token efficiency is a critical factor when working with GPT-5.5 and Claude Mythos/3.5, especially as task complexity and conversation length increase. In this section, we explore comprehensive strategies to optimize token usage without compromising output quality.
Techniques for Reducing Redundancy
- Use system-level instructions: Place generic guidelines in the system prompt to avoid repeating them in every user prompt.
- Leverage variables and placeholders: Use concise tags or variables to represent recurring entities or instructions within the conversation.
- Summarize context: Periodically summarize conversation history to keep memory concise.
Selective Context Inclusion
Instead of feeding the model entire datasets or lengthy documents, extract and include only the most relevant snippets. For example, in a security audit prompt, supply only critical code segments rather than entire files.
Prompt Compression and Paraphrasing
Rewriting verbose instructions into concise, semantically equivalent phrasing reduces tokens. Tools and scripts that paraphrase and compress prompts can automate this process at scale.
Utilizing Model-Specific Features
GPT-5.5 supports advanced token weighting and prioritization, allowing prompt engineers to emphasize or de-emphasize specific prompt parts. Claude Mythos/3.5 offers adaptive conditioning to dynamically modulate verbosity based on task importance.
Example: Token-Efficient Prompt Before and After
- Before: “Please generate a detailed Python script for web scraping the entire website, including handling pagination, error checking, and storing output in JSON format.”
- After: “Generate Python web scraper handling pagination and errors; output JSON.”
Despite the brevity, the refined prompt still guides the model effectively due to the reduced noise and clearer focus.
Prompt Chaining Methodologies: Architecting Complex AI Interactions
Prompt chaining is the cornerstone methodology enabling AI to tackle complex, multi-step tasks by decomposing them into manageable segments. This section explores various chaining architectures, design principles, and practical examples.
Simple Linear Chains
Linear chaining involves sequential prompts where each output feeds the next. This technique is useful for tasks such as multi-stage content writing or multi-layered code generation.
Hierarchical Chains
Hierarchical chaining organizes prompts into parent-child relationships. A parent prompt initiates a broad task, spawning child prompts that handle subtasks. For example, a parent prompt may request a research report outline, while child prompts generate individual sections.
Conditional Chains
Conditional chaining introduces decision logic based on prior outputs. For instance, if an AI detects a vulnerability in a code review prompt, it triggers a specialized mitigation prompt; otherwise, it proceeds to documentation generation.
Iterative and Feedback Loops
Iterative chains enable repeated refinement by looping outputs back into the model for improvement. This is critical for debugging code or polishing complex documents.
Implementation Best Practices
- Maintain consistent data formats across chain links to avoid parsing errors.
- Use unique identifiers and metadata for tracking prompt-output relationships.
- Monitor token consumption and truncate or summarize intermediate outputs to preserve token budgets.
- Incorporate error handling prompts to detect and correct model misinterpretations.
To further enhance your mastery of AI prompt design, the Comprehensive Prompt Chaining Guide offers an extensive collection of specialized ChatGPT prompt strategies and practical examples. This guide consolidates advanced techniques that complement the architectures discussed here, providing a deeper understanding of effective prompt sequencing for complex AI interactions.
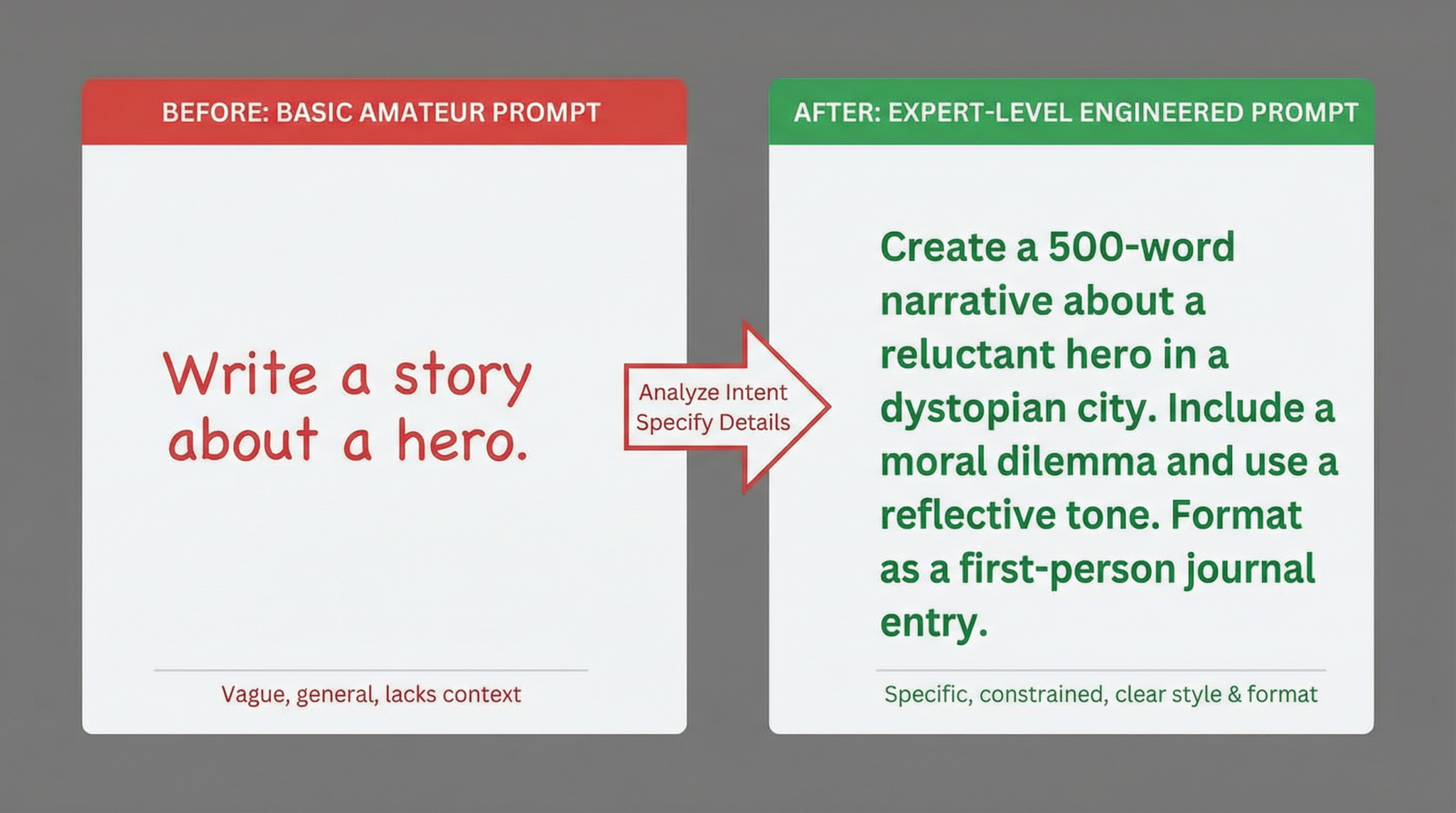
Before and After Examples: Transforming Prompts for Maximum Impact
Understanding how to refine prompts is best demonstrated through concrete examples. Below are detailed before-and-after prompt comparisons illustrating the power of advanced techniques across different use cases.
Example 1: Complex Coding Task
- Before: “Write a Python script to scrape data from a website.”
- After: “As a senior Python developer, generate an asynchronous Python 3.11 scraper using aiohttp to crawl all pages of the ‘example.com/products’ section with robust error handling and export results as a JSON file.”
The after prompt adds specificity about framework, concurrency, and output format, guiding the model to produce more practical code.
Example 2: Security Analysis
- Before: “Check this code for security issues.”
- After: “Analyze the following Node.js Express API code for OWASP Top 10 vulnerabilities, including injection and authentication flaws. Provide a prioritized list of detected issues with remediation advice.”
The enhanced prompt frames the task clearly and sets expectations for output structure and content depth.
Example 3: Multi-Agent Workflow Coordination
- Before: “Help automate a software development pipeline.”
- After: “Define roles for five AI agents in a software development pipeline: requirements analyst, architect, coder, tester, and security auditor. For each agent, provide detailed prompt instructions and the expected input/output format to enable seamless workflow orchestration.”
This transformation from vague to precise enables efficient multi-agent orchestration.
Example 4: Token Optimization
- Before: “Please provide a detailed explanation of the merge sort algorithm including complexity analysis and example code.”
- After: “Explain merge sort algorithm with complexity and Python example concisely.”
The after prompt reduces token usage while maintaining clarity, improving cost-efficiency.
Conclusion: Mastering Advanced Prompting in 2026 and Beyond
As AI language models continue to evolve, the sophistication of prompting techniques must keep pace. This handbook has unpacked advanced strategies for harnessing the full power of ChatGPT GPT-5.5 and Claude Mythos/3.5, focusing on complex coding, security analysis, and multi-agent orchestration. By integrating dozens of expertly crafted prompt templates, optimized token management tactics, and robust prompt chaining methodologies, practitioners can significantly elevate their AI-driven workflows.
We encourage professionals to continuously experiment with layered prompting, persona injection, and multi-agent coordination to discover innovative applications tailored to their domains. The future of AI prompting is dynamic, collaborative, and integrated—equipping yourself with these advanced techniques ensures you remain at the forefront of this transformative technology.
Access 40,000+ AI Prompts for ChatGPT, Claude & Codex — Free!
Subscribe to get instant access to our complete Notion Prompt Library — the largest curated collection of prompts for ChatGPT, Claude, OpenAI Codex, and other leading AI models. Optimized for real-world workflows across coding, research, content creation, and business.