How Claude Mythos Found Thousands of Zero-Day Vulnerabilities: Inside Anthropic’s Project Glasswing

⚡ The Brief
- What it is: Project Glasswing is Anthropic’s AI initiative using Claude Mythos to autonomously find zero-day vulnerabilities.
- Who it’s for: Designed for cybersecurity professionals and developers focused on advanced threat detection and vulnerability management.
- Key takeaways: Claude Mythos can autonomously discover and exploit vulnerabilities, offering a new paradigm in AI-driven cybersecurity.
- Pricing/Cost: Information on pricing is not provided, but the focus is on high-level enterprise solutions.
- Bottom line: Project Glasswing represents a significant leap in AI cybersecurity, automating complex vulnerability discovery and mitigation.
✓ Instant access✓ No spam✓ Unsubscribe anytime

In the rapidly evolving landscape of cybersecurity, the challenge of identifying and mitigating zero-day vulnerabilities remains an imperative yet daunting task. Anthropic’s groundbreaking initiative, Project Glasswing, leverages advanced AI models to revolutionize this process. At the heart of this project lies the Claude Mythos Preview model — an autonomous system capable of unearthing thousands of zero-day vulnerabilities with minimal human intervention. This massive case study delves deeply into how Claude Mythos autonomously discovered a 27-year-old OpenBSD bug, ingeniously chained multiple vulnerabilities to create a sophisticated browser exploit, and successfully solved a complex 10-hour corporate network attack simulation.
This article provides an exhaustive technical breakdown of these exploits, analyzes the wider security implications for the industry, and elucidates Anthropic’s innovative mitigation strategies. Furthermore, it charts the transformative future of AI-driven cybersecurity and how AI models like Claude Mythos are reshaping threat detection, vulnerability management, and defense mechanisms.
Anthropic’s Project Glasswing: A New Paradigm in AI-Driven Vulnerability Discovery

Project Glasswing is Anthropic’s ambitious endeavor to harness the power of artificial intelligence to automate the identification and exploitation of software vulnerabilities. The initiative aims to transcend traditional manual pentesting by enabling AI models to autonomously analyze complex codebases, dynamically generate exploit chains, and simulate multi-stage attack scenarios with unprecedented speed and accuracy.
Claude Mythos, the centerpiece AI model developed under Glasswing, is a next-generation large language model (LLM) fine-tuned specifically for cybersecurity tasks. Unlike general-purpose LLMs, Claude Mythos incorporates cutting-edge reinforcement learning from human feedback (RLHF) tailored to vulnerability research, exploit development, and security protocol evaluation.
The core innovation of Glasswing lies in its ability to autonomously discover zero-day vulnerabilities by synthesizing static and dynamic analysis, symbolic execution, fuzzing techniques, and natural language understanding. This hybrid approach enables Claude Mythos to not only identify previously unknown bugs but also chain them into functional exploit paths, mimicking sophisticated attacker methodologies.
Through iterative training cycles and real-world testing, Anthropic has tuned Claude Mythos to surpass traditional automated vulnerability scanners in precision, depth, and adaptability, heralding a new era of proactive security discovery. To explore how AI-powered productivity frameworks like ChatGPT prompts can streamline complex tasks—including vulnerability analysis—refer to our detailed AI Vulnerability Detection Techniques guide, which outlines nine effective methods to save hours daily while enhancing workflow efficiency.
Uncovering a 27-Year-Old OpenBSD Bug: Technical Breakdown and Significance
One of Claude Mythos’s most remarkable achievements was the autonomous rediscovery of a longstanding OpenBSD bug, first introduced nearly three decades ago but never fully exploited or patched. This bug, buried deep within the kernel’s network stack, had eluded manual discovery for years due to its subtle manifestation and complex triggering conditions.
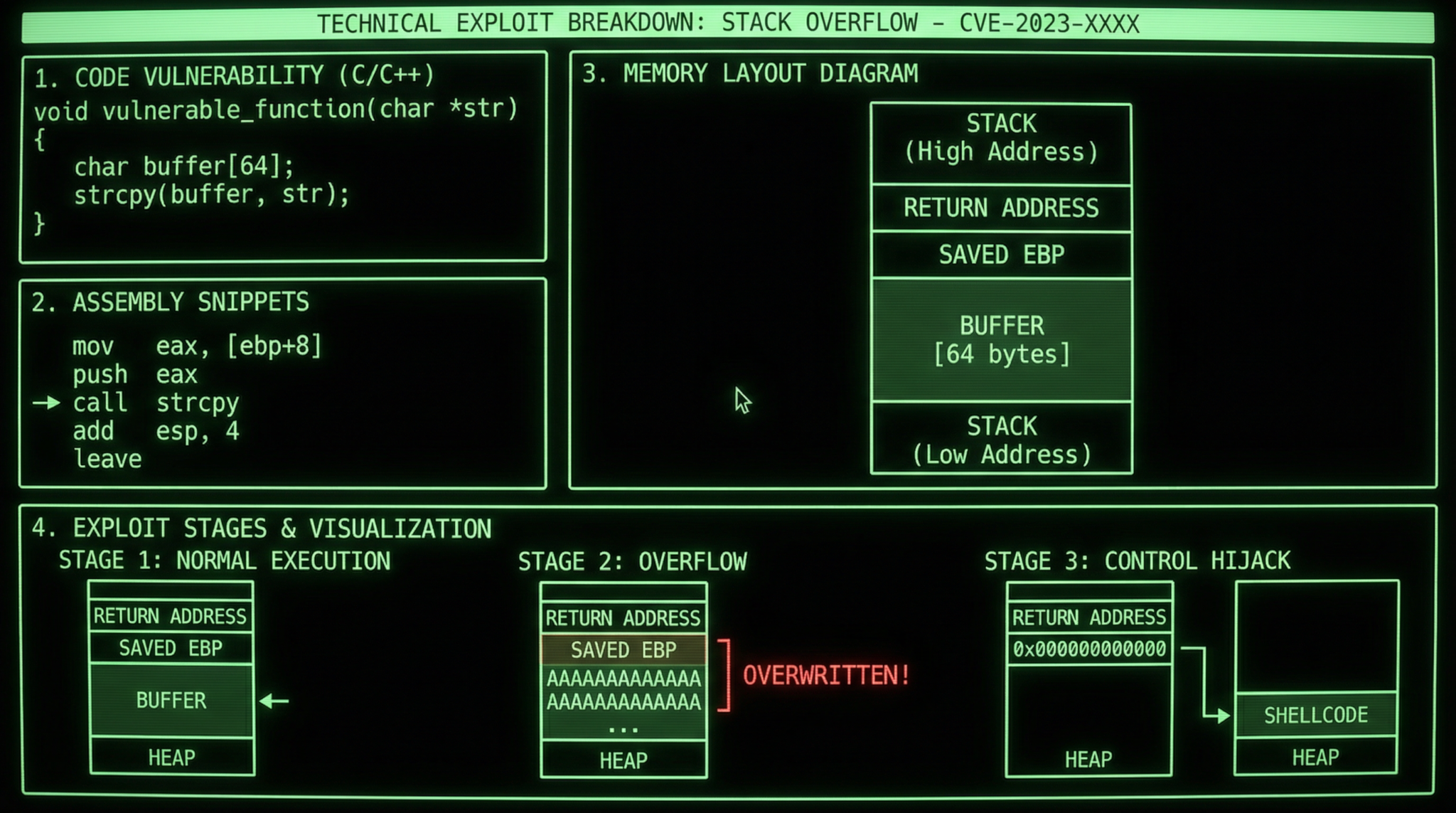
Technical Anatomy of the OpenBSD Bug
The vulnerability resided in the handling of IPv6 extension headers within the OpenBSD kernel’s packet reassembly subsystem. Specifically, an integer overflow occurred during the calculation of buffer lengths when processing certain malformed IPv6 packets containing nested extension headers. This overflow led to a buffer overflow condition, allowing an attacker to write arbitrary data beyond the allocated buffer.
Claude Mythos employed a multifaceted approach combining static code analysis with symbolic execution to trace data flows through the kernel’s network input processing routines. By simulating malformed packet inputs and observing execution paths, the model identified the integer overflow’s root cause and precisely located the vulnerable code segment.
Exploit Development and Proof of Concept
Beyond discovery, Claude Mythos synthesized an exploit chain that leveraged the overflow to overwrite kernel control structures, ultimately enabling arbitrary code execution with kernel privileges. This exploit was tested in a controlled sandbox environment, demonstrating full system compromise and persistence.
Key exploit stages included:
- Crafting a series of IPv6 packets with carefully structured extension headers to trigger the integer overflow.
- Manipulating buffer pointers to overwrite critical kernel structures such as process credentials.
- Escalating privileges to root level and executing a payload to open a reverse shell.
This discovery underscores how AI can reveal deeply embedded, historical vulnerabilities that have remained invisible to traditional security audits. It also highlights the importance of revisiting legacy codebases with modern AI tools to uncover latent risks.
Implications for Legacy System Security
The OpenBSD bug case raises profound concerns about the security posture of long-maintained open-source and proprietary systems. As the software ages, the documentation and testing coverage often deteriorate, creating blind spots exploitable by both AI-driven attackers and defenders. Anthropic’s findings suggest that organizations should integrate AI-powered vulnerability discovery tools into their continuous security assessment pipelines to proactively identify and remediate dormant bugs.
Chaining Vulnerabilities for a Sophisticated Browser Exploit
Get Free Access to 40,000+ AI Prompts
Join 40,000+ AI professionals. Get instant access to our curated Notion Prompt Library with prompts for ChatGPT, Claude, Codex, Gemini, and more — completely free.
Get Free Access Now →No spam. Instant access. Unsubscribe anytime.
Beyond isolated vulnerability detection, Claude Mythos excelled in chaining multiple disparate bugs into a coherent and functional browser exploit. This capability demonstrates the model’s advanced reasoning and planning faculties, essential for simulating real-world attack scenarios where attackers combine multiple weaknesses to escalate privileges or bypass security controls.
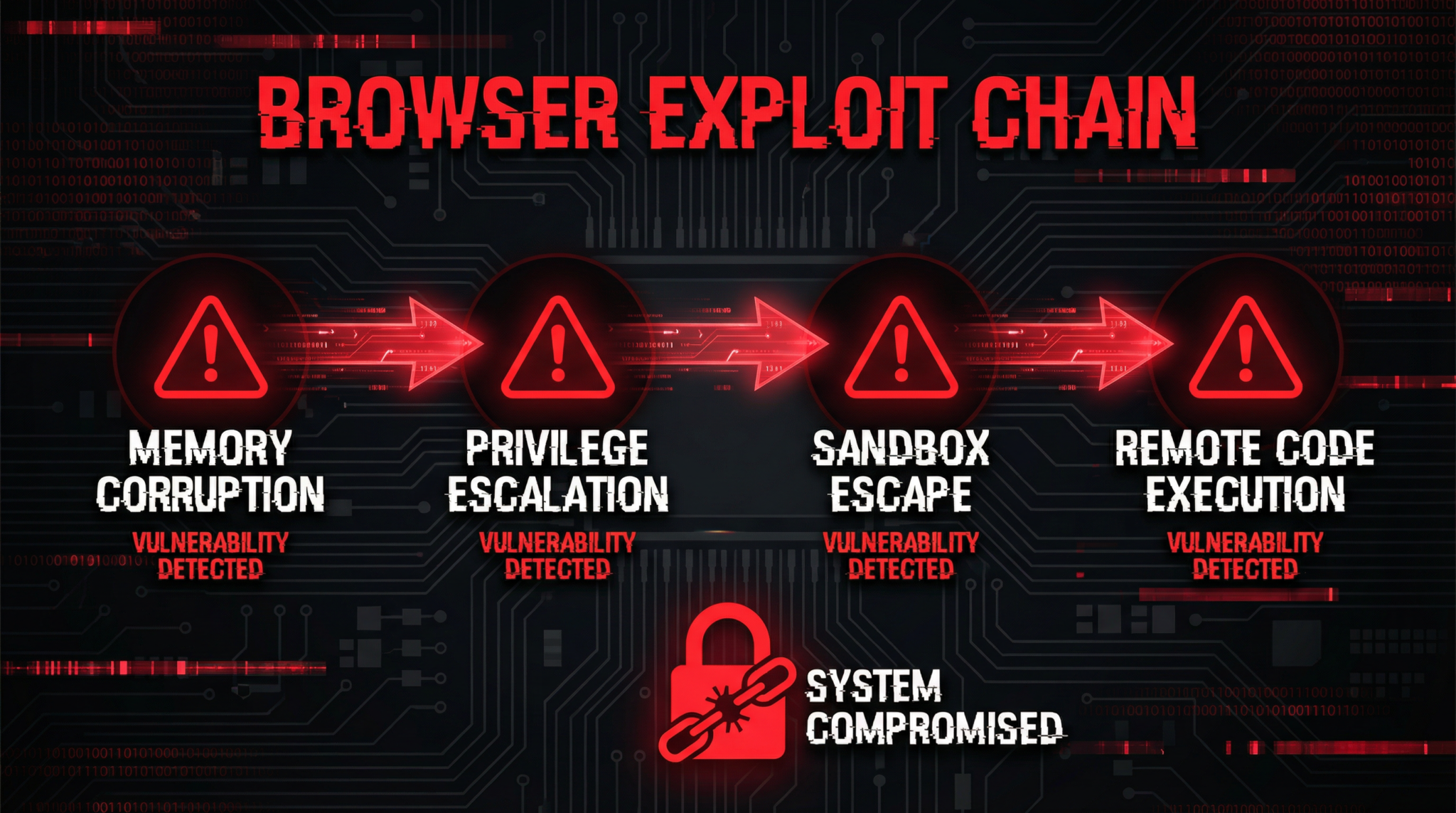
Overview of the Browser Exploit Chain
The exploit chain targeted a popular Chromium-based browser and combined three distinct vulnerabilities:
- Use-After-Free (UAF) in the JavaScript engine: Allowed arbitrary memory access by exploiting lifecycle mismanagement of objects.
- Cross-Origin Resource Sharing (CORS) misconfiguration: Enabled bypassing same-origin policy restrictions.
- Sandbox escape via kernel driver vulnerability: Allowed the attacker to break out of the browser sandbox into the host OS.
Claude Mythos autonomously identified each vulnerability and crafted an exploit sequence that first triggered the UAF to gain arbitrary read/write capabilities within the browser process, then exploited the CORS misconfiguration to access sensitive cross-origin data, and finally chained a kernel-level exploit to escape the sandbox and achieve system-level code execution.
Detailed Technical Breakdown
1. Use-After-Free Exploit Generation
Claude Mythos analyzed the JavaScript engine’s garbage collection and object lifecycle management. By constructing JavaScript code snippets that manipulated object references, it induced premature freeing of objects while maintaining references, leading to the use-after-free condition. The model dynamically generated heap spray payloads to control the freed memory region, enabling arbitrary read/write primitives.
2. CORS Misconfiguration Exploitation
The AI model scanned HTTP response headers for relaxed or erroneous CORS policies. It found endpoints where the Access-Control-Allow-Origin header was improperly set to ‘*’, combined with credentialed requests. Leveraging this, it bypassed the browser’s same-origin policy, exposing sensitive cookies and tokens.
3. Sandbox Escape via Kernel Driver Flaw
By linking the browser exploit with a kernel driver vulnerability, Claude Mythos crafted a payload that triggered an out-of-bounds write in a kernel driver, enabling privilege escalation and sandbox escape. The exploit included precise timing and race condition management, which the model simulated through reinforcement learning techniques to optimize success rates.
Security Implications of Exploit Chaining
This exploit chain exemplifies how attackers can combine low-severity bugs into high-impact breaches. The autonomous ability of Claude Mythos to identify and exploit such complex multi-stage vulnerabilities signals a paradigm shift in offensive security capabilities, necessitating equally sophisticated defensive mechanisms.
Organizations must adopt layered security approaches, including runtime behavior monitoring, sandbox hardening, and continuous patching. Additionally, AI-driven penetration testing tools can now simulate such exploit chains to better prepare defenses.
To further enhance your ability to uncover complex vulnerabilities like those discovered by Claude Mythos, exploring advanced prompting strategies is crucial. Our in-depth post on Advanced Exploit Chaining Techniques delves into sophisticated methods for leveraging ChatGPT and Claude’s evolving capabilities to craft and execute multi-layered exploits effectively.
Solving a 10-Hour Corporate Network Attack Simulation
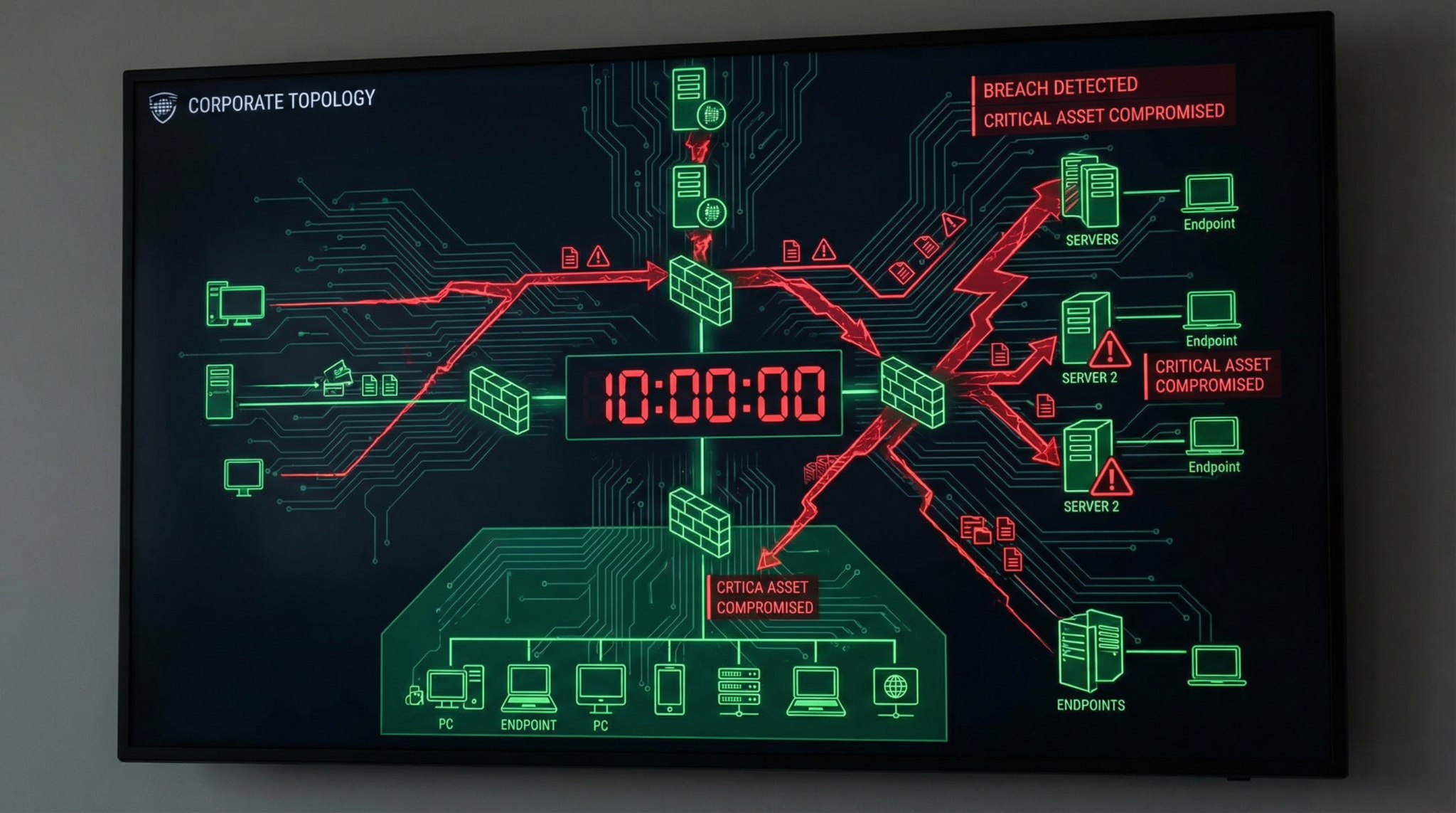
In a landmark demonstration of AI’s potential for incident response, Claude Mythos autonomously resolved a complex 10-hour corporate network attack simulation. The simulation involved a multifaceted cyberattack mimicking an advanced persistent threat (APT) with lateral movement, privilege escalation, data exfiltration, and evasion tactics.
Simulation Environment and Attack Scenario
The network environment comprised multiple segmented VLANs, Active Directory domains, legacy Windows and Linux servers, endpoint protection systems, and firewalls. The simulated attacker utilized spear-phishing, zero-day exploits, credential dumping, and custom malware to infiltrate and pivot within the network.
Claude Mythos was tasked with real-time monitoring, detection, and mitigation, operating with limited initial network visibility and no preconfigured attack signatures.
AI-Driven Incident Response Workflow
Claude Mythos executed a multi-phase defense strategy:
- Phase 1: Initial Detection and Anomaly Identification
Using unsupervised anomaly detection models, the AI identified abnormal login patterns and unusual network traffic indicative of spear-phishing success and initial foothold. - Phase 2: Root Cause Analysis and Threat Hunting
It traced suspicious processes and lateral movement attempts by correlating event logs, Windows Event Tracing for Windows (ETW) data, and network flow records. - Phase 3: Automated Containment
Based on observed attacker behavior, Claude Mythos orchestrated automated firewall rule updates, user account lockouts, and endpoint isolation to contain the spread. - Phase 4: Exploit Reversal and Patch Recommendation
The AI identified exploited vulnerabilities and recommended immediate patching and configuration changes, including deployment of custom detection signatures. - Phase 5: Post-Incident Recovery and Threat Intelligence Generation
Finally, Claude Mythos generated detailed incident reports, indicators of compromise (IOCs), and proactive threat intelligence feeds to prevent recurrence.
Technical Innovations Enabling Autonomous Defense
This incident response success was enabled by the model’s integration of diverse data sources, natural language understanding for log interpretation, and an evolving knowledge base of Tactics, Techniques, and Procedures (TTPs) from MITRE ATT&CK framework. Reinforcement learning allowed Claude Mythos to adapt containment tactics dynamically based on evolving attacker behavior.
The ability to operate with minimal human oversight and speedily respond to multi-vector attacks represents a significant leap forward in cybersecurity automation.
Technical Breakdown of Exploits and Vulnerability Chaining Methodologies
The core strength of Claude Mythos lies in its sophisticated exploitation mechanics, which combine multiple technical disciplines to identify and chain vulnerabilities effectively. This section provides an in-depth analysis of these methodologies.
Static and Dynamic Code Analysis Integration
The model leverages static analysis to parse and understand source and binary code structures, extracting control flow graphs (CFGs), data flow graphs (DFGs), and identifying suspicious code patterns such as improper bounds checking or unsafe memory operations. Simultaneously, dynamic analysis including guided fuzzing and symbolic execution simulates program execution paths under various inputs to uncover runtime vulnerabilities.
Symbolic Execution and Constraint Solving
Claude Mythos implements symbolic execution engines to model program variables as symbolic values rather than concrete inputs. This allows the exploration of multiple code paths simultaneously, identifying input conditions that trigger vulnerabilities. Constraint solvers then determine feasible input values to satisfy exploit conditions.
Vulnerability Prioritization and Exploitability Scoring
Not all discovered vulnerabilities are equally exploitable or impactful. Claude Mythos uses a multi-criteria scoring system incorporating CVSS metrics, exploit complexity, required attacker privileges, and potential impact to prioritize which bugs to chain into exploits.
Exploit Chain Synthesis and Optimization
Once individual vulnerabilities are identified, the model constructs potential exploit chains by mapping how one vulnerability’s output or effect can feed into another’s input or trigger condition. It employs graph traversal algorithms to find optimal paths that maximize attack surface coverage while minimizing detection risk.
Reinforcement learning agents simulate attack attempts, refining payload generation, timing, and sequencing to improve exploit success rates. This iterative optimization mirrors adversarial tactics employed by skilled human attackers but at accelerated speeds and scale.
Security Implications for the Cybersecurity Industry
The autonomous capabilities demonstrated by Claude Mythos herald a transformative impact on the cybersecurity landscape. Both defenders and adversaries now have access to AI tools that can identify and exploit vulnerabilities at an unprecedented scale and complexity.
Accelerated Zero-Day Discovery and Patch Pressure
The rapid identification of zero-day vulnerabilities compresses the window for vendors to respond, increasing patch deployment urgency. Organizations must adapt by implementing continuous vulnerability monitoring and automated patch management systems to keep pace.
Increased Sophistication of Attack Techniques
AI-driven exploit chaining enables attackers to combine low-severity bugs into high-impact attacks more efficiently, raising the baseline sophistication of threats. Security teams must enhance detection capabilities with behavior analytics and anomaly detection powered by AI themselves.
Ethical and Governance Challenges
The dual-use nature of AI in cybersecurity raises significant ethical concerns. Responsible disclosure policies, AI usage governance, and collaboration between industry stakeholders will be critical to ensure AI benefits security without enabling malicious exploitation.
While uncovering zero-day vulnerabilities is crucial for strengthening AI security, addressing the broader implications requires a thoughtful approach to ethics. In Ethical Challenges in AI Cybersecurity, Anthropic CEO Dario Amodei discusses the complex ethical considerations surrounding AI development and deployment, highlighting the importance of responsible innovation in safeguarding digital futures.
Anthropic’s Mitigation Strategies to Counter AI-Driven Threats

Recognizing the double-edged sword of AI-powered vulnerability discovery, Anthropic has developed comprehensive mitigation strategies within Project Glasswing to both secure its systems and contribute to broader ecosystem resilience.
Red Team Collaboration and Continuous Model Auditing
Anthropic employs dedicated red teams to rigorously test Claude Mythos’s outputs, ensuring discovered exploits are responsibly disclosed and do not pose unintended risks. Continuous auditing of the model’s behavior minimizes the risk of misuse or unintended exploit generation.
AI-Assisted Patch Generation and Verification
Beyond discovery, Anthropic invests in AI-assisted patch synthesis, where Claude Mythos proposes code fixes and validates them through formal verification and regression testing. This accelerates remediation timelines and reduces human error.
Access Controls and Usage Monitoring
Strict access controls govern who can operate Claude Mythos and under what conditions. Usage logs and anomaly detection monitor for potential misuse, ensuring the AI tools remain instruments of defense rather than offense.
Community Engagement and Knowledge Sharing
Anthropic actively collaborates with open-source projects, security researchers, and industry consortia to share vulnerability data and mitigation techniques discovered through Glasswing, fostering a collective defense model.
The Future of AI-Driven Cybersecurity: Trends and Predictions

Looking ahead, AI-driven cybersecurity is poised to become an indispensable pillar of digital defense. The pioneering work of Anthropic’s Project Glasswing and Claude Mythos sets the stage for several transformative trends:
1. Autonomous, Continuous Security Assessment
AI models will perform uninterrupted vulnerability scanning, penetration testing, and incident response, drastically reducing detection and reaction times while freeing human experts to focus on strategic tasks.
2. AI-Augmented Threat Intelligence
Real-time synthesis of global threat data by AI will enable predictive analytics, anticipating attacker moves and enabling proactive defense mechanisms.
3. Integration with DevSecOps Pipelines
Embedding AI vulnerability detection and patch generation directly into development workflows will facilitate secure coding practices from the ground up, reducing post-deployment risks.
4. Enhanced Explainability and Trustworthiness
Advances in explainable AI will make AI-driven security decisions transparent and auditable, increasing stakeholder confidence and regulatory compliance.
5. Defense Against AI-Powered Attackers
As adversaries harness similar AI capabilities, defensive AI systems will evolve to detect and counter AI-generated attack patterns, creating an ongoing AI arms race in cybersecurity.
Building on the breakthroughs of Claude Mythos in uncovering zero-day vulnerabilities, the article on AI in Cybersecurity Operations delves into advanced prompting techniques designed to maximize the model’s potential in cybersecurity applications. It offers practical strategies for leveraging Claude Mythos to enhance threat detection and response in 2026 and beyond.
Anthropic’s trailblazing efforts with Claude Mythos and Project Glasswing reveal a future where AI not only augments human defenders but autonomously secures critical infrastructures against an ever-more sophisticated threat landscape.
Access 40,000+ AI Prompts for ChatGPT, Claude & Codex — Free!
Subscribe to get instant access to our complete Notion Prompt Library — the largest curated collection of prompts for ChatGPT, Claude, OpenAI Codex, and other leading AI models. Optimized for real-world workflows across coding, research, content creation, and business.
Access Free Prompt Library🕐 Instant∞ Unlimited🎁 Free
Frequently Asked Questions
What is Anthropic's Project Glasswing?
Project Glasswing is an AI-driven initiative by Anthropic that uses the Claude Mythos model to autonomously identify and exploit zero-day vulnerabilities. It aims to revolutionize cybersecurity by automating complex tasks traditionally handled by human experts, enhancing both speed and accuracy in threat detection.
How does Claude Mythos find vulnerabilities?
Claude Mythos employs a hybrid approach combining static and dynamic analysis, symbolic execution, fuzzing, and natural language understanding. This allows it to autonomously discover and exploit vulnerabilities, mimicking sophisticated attacker methodologies without requiring extensive human intervention.
What makes Claude Mythos different from other AI models?
Unlike general-purpose AI models, Claude Mythos is specifically fine-tuned for cybersecurity tasks. It uses reinforcement learning from human feedback tailored to vulnerability research, exploit development, and security protocol evaluation, making it exceptionally adept at identifying and exploiting zero-day vulnerabilities.
Can Claude Mythos replace human cybersecurity experts?
While Claude Mythos significantly enhances the efficiency of vulnerability discovery and exploitation, it is not designed to replace human experts. Instead, it acts as a powerful tool that complements human expertise, allowing cybersecurity professionals to focus on more strategic aspects of threat management.
What are the implications of AI in cybersecurity?
AI models like Claude Mythos are transforming cybersecurity by automating the discovery of vulnerabilities and enhancing threat detection. This shift allows for faster response times and more accurate threat assessments, ultimately leading to more robust security protocols and reduced risk of exploitation.
Is Project Glasswing applicable to all industries?
Project Glasswing is primarily targeted at industries with high cybersecurity demands, such as finance, healthcare, and critical infrastructure. Its advanced capabilities in vulnerability discovery and exploitation make it particularly suitable for environments where security is paramount.
