How to Set Up GPT-5.5 Trusted Access for Cyber: A Complete Security Workflow Tutorial
Author: Markos Symeonides
On May 7, 2026, OpenAI expanded its Trusted Access for Cybersecurity (TAC) program with the release of GPT-5.5 and the specialized GPT-5.5-Cyber model. This exclusive program empowers verified cyber defenders across critical infrastructure sectors with advanced AI-driven cybersecurity capabilities, fortified by stringent safeguards designed specifically for defensive operations.
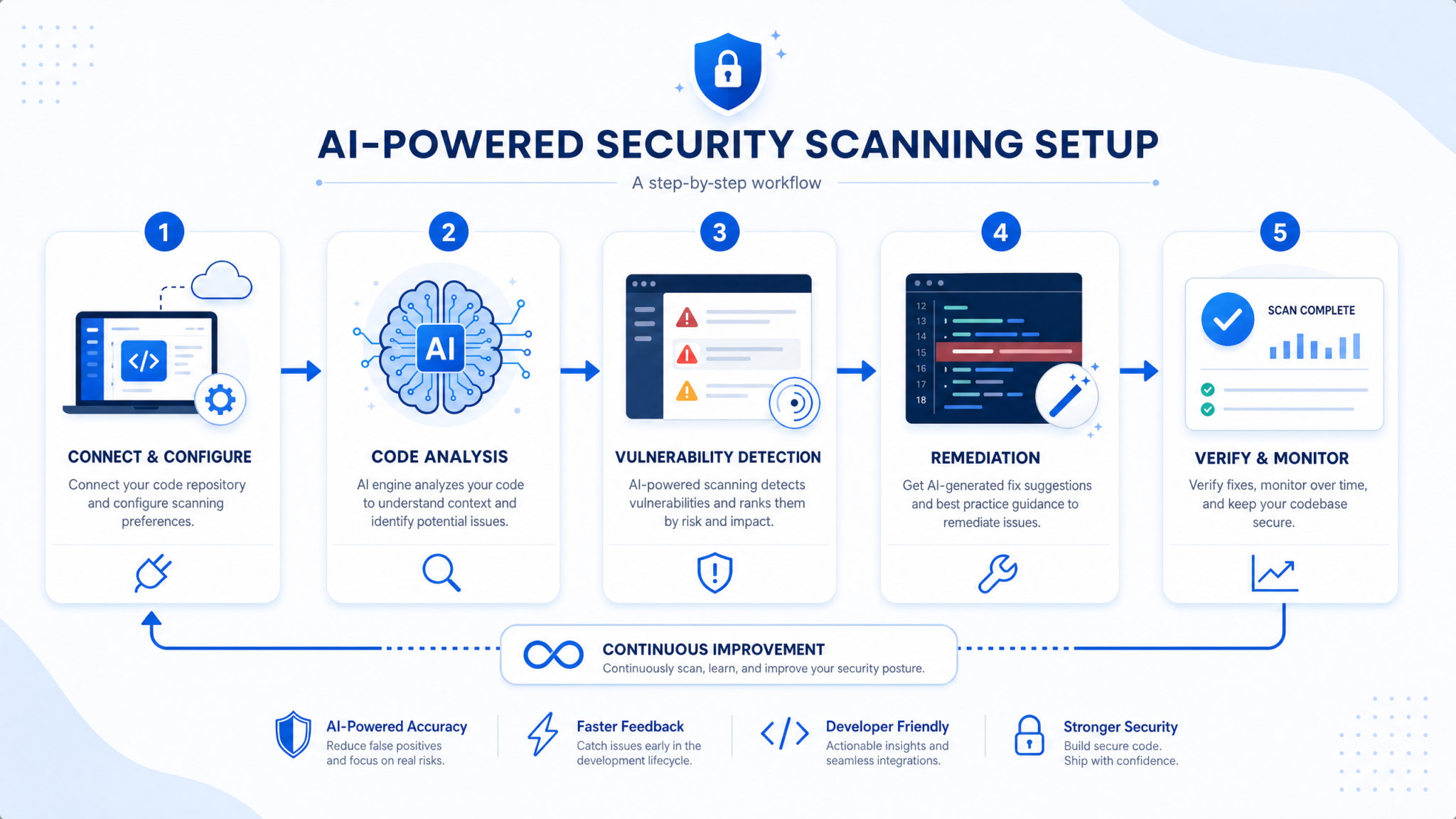
This comprehensive tutorial offers a step-by-step guide to setting up, configuring, and utilizing GPT-5.5 Trusted Access for Cyber effectively. By integrating this cutting-edge AI model into your security workflows, your organization can significantly enhance vulnerability management, accelerate incident response, and strengthen overall cyber defense posture against increasingly sophisticated threats.
1. Understanding TAC Eligibility Requirements
The TAC program maintains a highly selective eligibility process to ensure that GPT-5.5’s advanced cybersecurity features are accessed responsibly by organizations with mature security operations. As of mid-2026, eligibility is restricted to verified entities operating within the following critical sectors:
- Financial Services: Banks, insurance companies, payment processors, and other financial institutions under strict regulatory oversight.
- Telecommunications: Providers managing essential communication infrastructure, including data transmission networks and mobile operators.
- Energy: Utilities and operators of power grids, renewable energy facilities, oil and gas production, and distribution systems.
- Public Services: Government agencies and organizations managing vital public infrastructure and services.
Geographically, eligibility now extends to European organizations, following OpenAI’s May 12, 2026 announcement, reflecting a commitment to strengthening global cybersecurity collaboration and resilience.
To qualify for TAC access, organizations must demonstrate the following core capabilities:
- Robust Cybersecurity Operations and Governance: Alignment with industry-leading frameworks such as NIST Cybersecurity Framework, ISO 27001, or equivalent standards.
- Compliance with Data Protection Regulations: Adherence to legal mandates like GDPR, CCPA, or relevant sector-specific privacy laws ensuring data confidentiality and integrity.
- Secure AI Access Management: Implementation of controls to monitor, restrict, and audit GPT-5.5 TAC usage within organizational environments.
Recognizing and preparing for these prerequisites upfront will facilitate a smoother application process and ensure seamless integration of GPT-5.5 TAC capabilities into your cybersecurity infrastructure.
2. Applying for Verified Defender Status
Obtaining verified defender status is a mandatory step to gain access to GPT-5.5 TAC resources. The application process is designed to rigorously assess your organization’s cybersecurity maturity, operational readiness, and commitment to responsible AI use through multiple stages:
- Registration: Establish an organizational profile on OpenAI’s TAC portal, providing detailed information about your cybersecurity teams, infrastructure, certifications, and security policies.
- Security Assessment: OpenAI’s cybersecurity experts conduct an in-depth evaluation of your existing controls, including incident response capabilities, vulnerability management practices, and data governance frameworks.
- Verification Interview: Key security leaders engage in a structured interview to discuss operational maturity, AI risk mitigation strategies, and regulatory compliance adherence.
- Approval and Onboarding: Upon successful verification, your organization receives API credentials, detailed onboarding documentation, and secure access to the GPT-5.5-Cyber environment.
This verification process can take several weeks depending on organizational complexity. Proactive preparation and transparent communication with OpenAI can help expedite approval.
For additional insights on AI workflow automation aligned with TAC, explore our in-depth guide: How to Use OpenAI Codex Memory and Scheduled Automations for Persistent AI Workflows.
3. Configuring GPT-5.5-Cyber for Your Environment
GPT-5.5-Cyber is tailored to augment cybersecurity teams by delivering advanced code analysis, exploit reasoning, and remediation prioritization. To maximize its effectiveness, adhere to these key configuration best practices:
- API Key Security: Securely store GPT-5.5 TAC API keys using enterprise-grade secrets management systems or hardware security modules (HSMs). Enforce automated key rotation policies to mitigate exposure risks.
- Model Parameter Customization: Fine-tune model sensitivity and confidence thresholds to balance detection accuracy and false positive rates, optimizing alert relevance.
- Seamless Data Integration: Connect GPT-5.5-Cyber with your Continuous Integration/Continuous Deployment (CI/CD) pipelines, source code management platforms (e.g., GitHub, GitLab), and vulnerability intelligence databases to enable real-time contextual analysis.
- Role-Based Access Controls (RBAC): Implement strict access policies ensuring only authorized cybersecurity personnel can interact with the AI model outputs and configurations.
OpenAI’s Daybreak platform provides an intuitive centralized interface for managing GPT-5.5 deployments, configuring workflows, and monitoring AI-generated security alerts, streamlining operational oversight.
4. Setting Up Effective Vulnerability Research Workflows
Utilizing GPT-5.5-Cyber’s powerful reasoning capabilities enables security teams to design targeted, automated workflows for vulnerability research, assessment, and remediation prioritization. Essential components include:
- Automated Dependency and Code Change Inspection: Continuously analyze codebase dependencies and commits for newly introduced vulnerabilities using AI-driven scanning.
- Exploitability Assessment: Leverage GPT-5.5-Cyber’s contextual analysis to determine whether identified vulnerabilities are realistically exploitable within your software ecosystem.
- Remediation Prioritization: Generate ranked vulnerability lists based on factors such as exploitability, potential business impact, and asset criticality to optimize patch management efforts.
- Comprehensive Vulnerability Surface Reporting: Produce detailed vulnerability reports featuring remediation progress, historical trends, and actionable security posture insights.
These AI-powered workflows can be integrated seamlessly with existing ticketing systems like Jira or ServiceNow and case management platforms, significantly boosting Security Operations Center (SOC) efficiency and response speed.
5. Integrating GPT-5.5-Cyber with Existing Security Tools (SIEM, SOAR)
Embedding GPT-5.5-Cyber insights into Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms amplifies AI’s impact by enabling real-time threat intelligence and automated remediation. Key integration strategies include:
- API-Driven Data Exchange: Push vulnerability analyses and remediation tasks into SIEM dashboards such as Splunk, IBM QRadar, or ArcSight to unify monitoring and alerting.
- Automated Playbook Execution: Configure SOAR tools (e.g., Palo Alto Cortex XSOAR, Demisto) to trigger incident response playbooks based on GPT-5.5-Cyber’s exploitability assessments, accelerating threat mitigation.
- Alert Context Enrichment: Enhance security alerts with AI-generated explanations detailing vulnerability severity, recommended remediation steps, and potential risk vectors to aid rapid analyst decision-making.
- Compliance and Audit Logging: Maintain comprehensive logs of AI interactions and automated actions to satisfy governance policies and regulatory audit requirements.
Notably, OpenAI’s recent partnership with Sophos enables customers to integrate GPT-5.5-Cyber threat intelligence directly into Sophos security management consoles, streamlining detection and remediation workflows across hybrid environments.
6. Best Practices for Responsible and Effective Defensive AI Usage
To fully leverage GPT-5.5 TAC capabilities while minimizing operational risks, organizations should adopt the following best practices:
- Human-in-the-Loop Validation: Ensure cybersecurity analysts review AI-generated findings before enacting remediation actions to reduce false positives and prevent unintended disruptions.
- Regular Model Updates and Fine-Tuning: Continuously update model parameters to adapt to emerging threat landscapes, newly discovered vulnerabilities, and organizational changes.
- Data Privacy and Security Compliance: Encrypt all sensitive data, including code, vulnerability information, and incident reports, both at rest and in transit, conforming to internal policies and regulatory frameworks.
- Comprehensive Training and Awareness: Educate security teams on GPT-5.5-Cyber’s capabilities, limitations, and best use practices to foster effective collaboration between human experts and AI.
- Incident Response Integration: Incorporate AI-generated insights into incident response playbooks to accelerate threat detection, investigation, and containment workflows.
For advanced tactics in AI-driven cybersecurity, review our specialized resource: Prompting GPT-5.5 for Cybersecurity: Vulnerability Research and Detection Rule Engineering Techniques.
7. Monitoring, Auditing, and Compliance Considerations
Ongoing monitoring and compliance management are vital for maintaining trust, security, and regulatory adherence when deploying GPT-5.5 TAC. Focus your efforts on the following areas:
- Comprehensive Usage Auditing: Log all AI queries, responses, user interactions, and remediation activities to create detailed audit trails for internal reviews and regulatory compliance.
- Performance and Effectiveness Metrics: Continuously track detection accuracy, false positive and negative rates, and remediation success metrics to iteratively improve AI-driven workflows.
- Regulatory Compliance Management: Ensure alignment with sector-specific cybersecurity regulations including the European NIS2 Directive, U.S. cybersecurity frameworks (e.g., CISA guidelines), and financial industry mandates.
- Access Rights and Permissions Review: Periodically audit user permissions, promptly revoking TAC access for personnel who no longer require it to minimize insider risks.
- AI Incident Reporting Protocols: Establish clear procedures for reporting AI-related anomalies or incidents to OpenAI and relevant oversight bodies to support transparency and continuous improvement.
OpenAI’s Daybreak platform simplifies governance through built-in compliance dashboards, real-time usage analytics, and customizable reporting tailored to TAC environments.
8. Future-Proofing Your GPT-5.5 TAC Deployment
As cyber threats evolve rapidly, maintaining an adaptable and scalable GPT-5.5 TAC deployment is critical. Consider these strategies to future-proof your AI-enhanced cybersecurity operations:
- Scalable Architecture: Design your TAC integration to support increasing data volumes and expanding use cases without degradation in performance.
- Multi-Model Collaboration: Combine GPT-5.5-Cyber with complementary AI models focused on anomaly detection, behavioral analytics, and threat hunting for holistic defense.
- Continuous Skill Development: Invest in ongoing AI and cybersecurity training programs to keep your teams proficient in leveraging evolving AI capabilities.
- Community Engagement: Actively participate in TAC user forums, threat intelligence sharing groups, and OpenAI’s cybersecurity ecosystem to stay informed on best practices and emerging threats.
By adopting these forward-looking practices, your organization will maximize the long-term value and security impact of GPT-5.5 Trusted Access for Cyber.
Conclusion: Empowering Cyber Defenders with GPT-5.5 Trusted Access
OpenAI’s GPT-5.5 Trusted Access for Cyber program represents a groundbreaking advancement in AI-augmented cybersecurity defense. By following this detailed tutorial, eligible organizations can:
- Successfully apply for verified defender status and gain exclusive access to TAC resources.
- Configure the GPT-5.5-Cyber model to align with their unique threat environment and operational needs.
- Integrate AI-driven vulnerability analysis, exploitability reasoning, and remediation prioritization seamlessly into established security operations and tooling.
- Implement continuous monitoring, auditing, compliance management, and responsible AI usage best practices to safeguard critical infrastructure.
When combined with expert human oversight and strong security governance, GPT-5.5 TAC empowers cyber defenders to proactively detect, analyze, and mitigate sophisticated threats at scale—ultimately bolstering organizational resilience against evolving adversaries.
For continued learning and practical hands-on tutorials related to OpenAI’s cybersecurity AI tools, explore Boost Productivity with OpenAI Codex in Parallel Development for advanced integration strategies and workflow optimizations.