GPT-5.5 Mini Prompts Masterclass: Optimizing Token Efficiency for High-Volume Applications
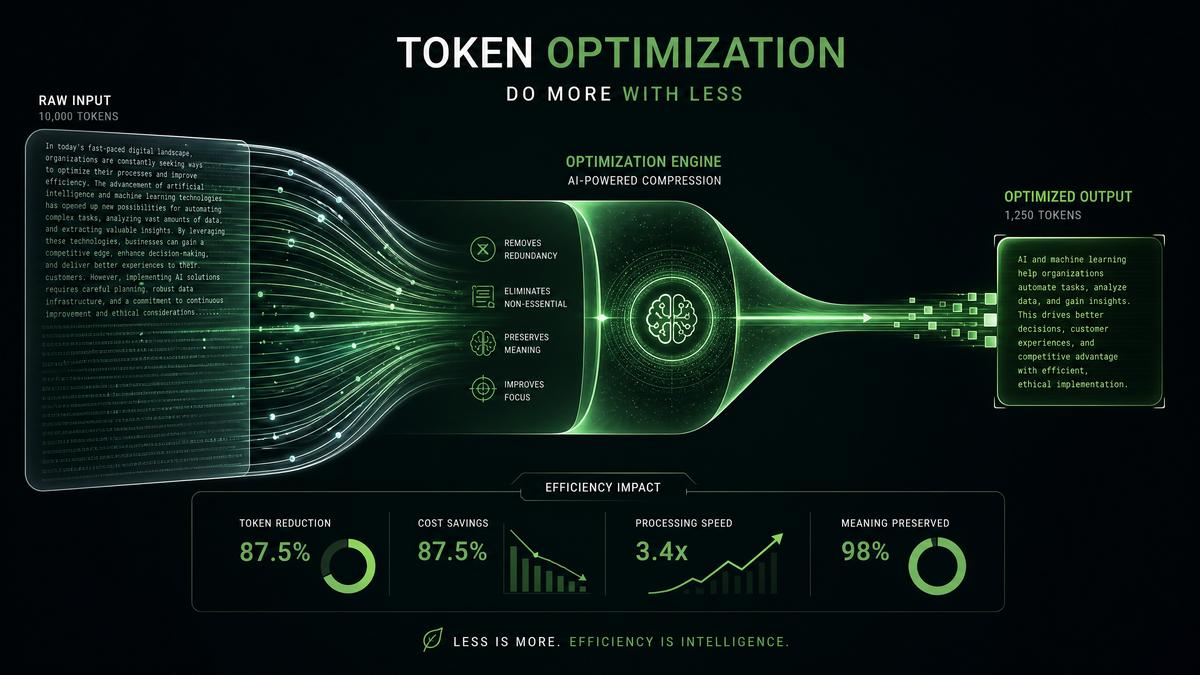
Introduction to GPT-5.5 Mini: Unlocking Cost-Effective High-Volume AI The GPT-5.5 Mini model represents a significant leap in AI accessibility for enterprises and developers aiming to deploy natural language processing (NLP) at scale without incurring prohibitive costs. Priced at approximately $5 per million input tokens and $25 per million output tokens,…